![Firepower Management Center Configuration Guide, Version 6.0 - Application Layer Preprocessors [Cisco Secure Firewall Management Center] - Cisco Firepower Management Center Configuration Guide, Version 6.0 - Application Layer Preprocessors [Cisco Secure Firewall Management Center] - Cisco](https://www.cisco.com/c/dam/en/us/td/i/300001-400000/370001-380000/371001-372000/371939.tif/_jcr_content/renditions/371939.jpg)
Firepower Management Center Configuration Guide, Version 6.0 - Application Layer Preprocessors [Cisco Secure Firewall Management Center] - Cisco
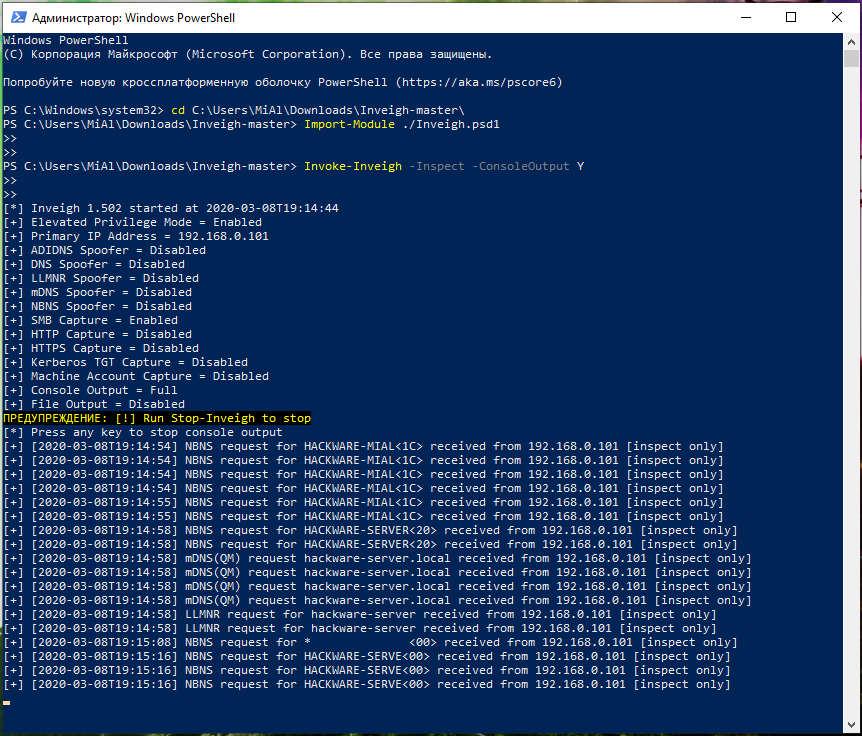
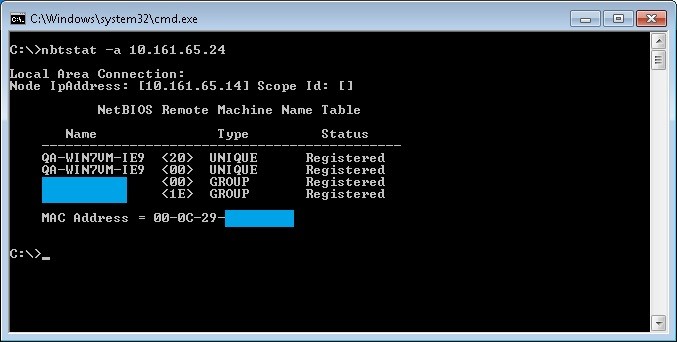
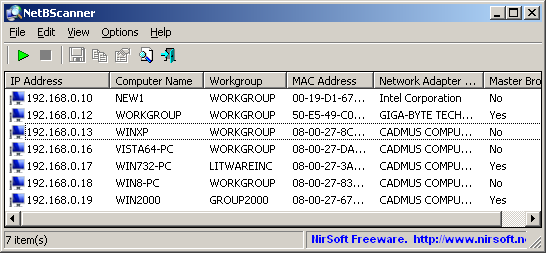
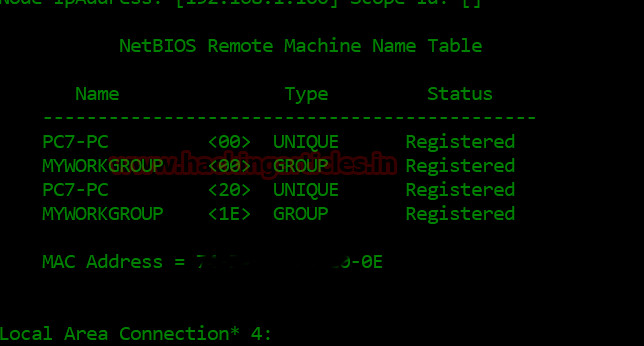
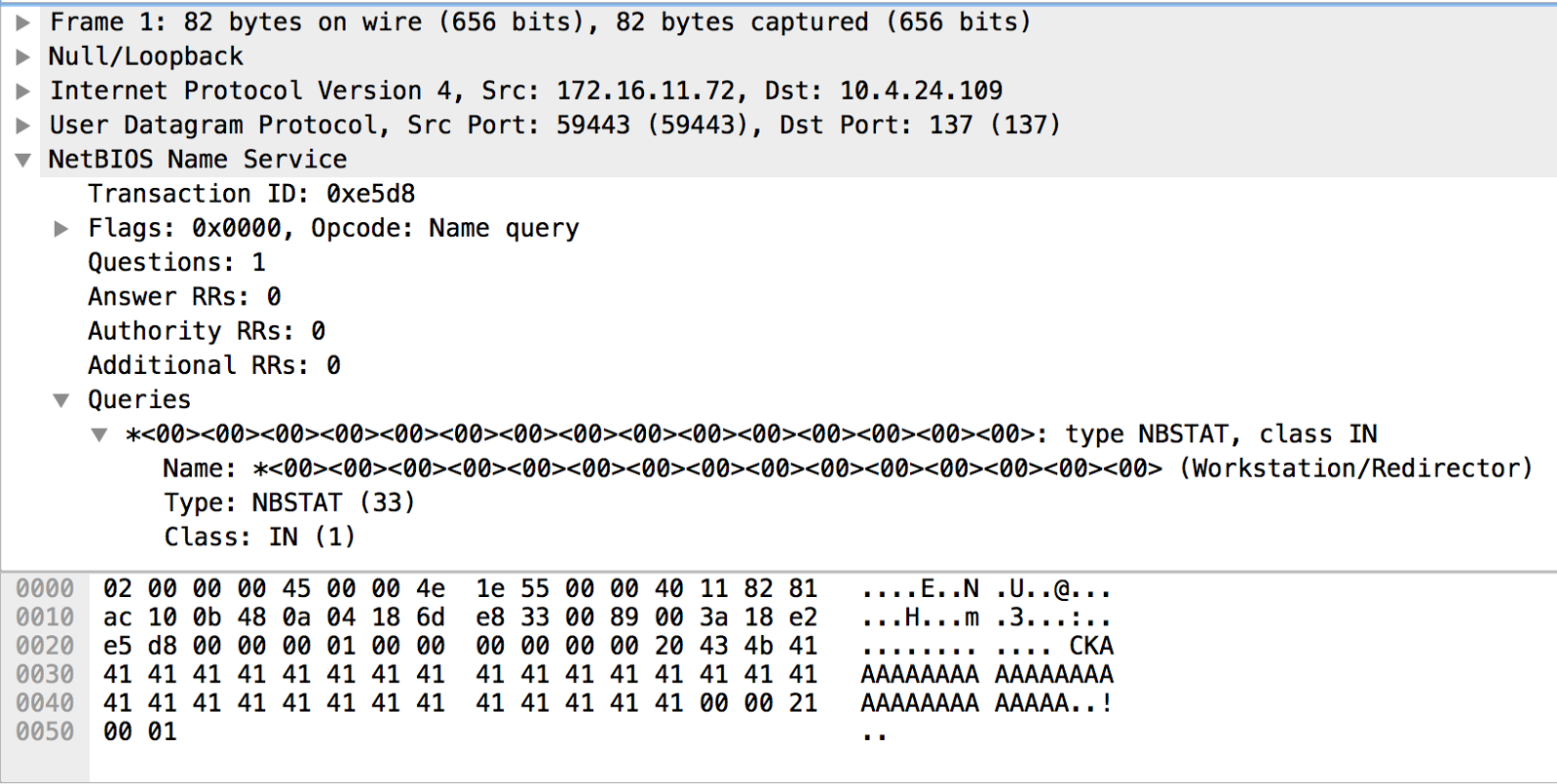
NetBIOS: what it is, how it works and how to use in information security - Ethical hacking and penetration testing